I’m David and this is Don’t Get Dead. Your information pathway to a more safe and more secure life experience. Tips on staying alive and keeping your possessions in a dangerous world. Paid subscribers obtain on-demand access to me as their personal or business security consultant. Get quick answers or in-depth discussions about any security or safety issues of concern. It’s a cost-effective way to utilize professional security expertise as you need it at your home or business.
This episode is about the terrorist attack cycle and what you can do about it. Why should you even be concerned about that? Because terrorism happens and it can happen to you. I live near NAS Pensacola where on December 9, 2019, a Saudi flight student took the lives of 3 sailors and injured 8 others. The Escambia County Sheriff’s Office responded to the attack and killed the shooter in just 8 minutes.
The speed of the response and the quick resolution to the event was the result of mental preparation and regular active shooter training by the deputies. In a later episode, we will address an updated civilian active shooter response called COPE. Cover, Observe, Plan, Execute. But this podcast is devoted to the process that terrorists utilize to formulate an attack. By learning what to look for you may be able to prevent a terrorist group from carrying out a heinous incident.
Terrorist attacks can take many forms, motivated by a variety of ideological, political, or religious beliefs. Some common types of terrorist attacks include:
1. Bombings involve the use of explosives to cause destruction and casualties.
2. Assassinations are the targeted killing of an individual or group of individuals.
3. Kidnappings: This type of attack involves the abduction of an individual or group of individuals for ransom or other purposes.
4. Hijackings are the takeover of a vehicle or other mode of transportation.
5. Cyber attacks vector the use of computer systems and networks to disrupt or damage critical infrastructure or steal sensitive information.
6. Mass shootings are intended to kill or injure a large number of people in a populated area.
7. Chemical or biological attacks utilize toxic or infectious agents to harm or kill people.
8. Attacks against the electrical grid.
It's important to note that terrorist attacks can be perpetrated by individuals or groups and can occur in any location, including urban areas, rural areas, and online.
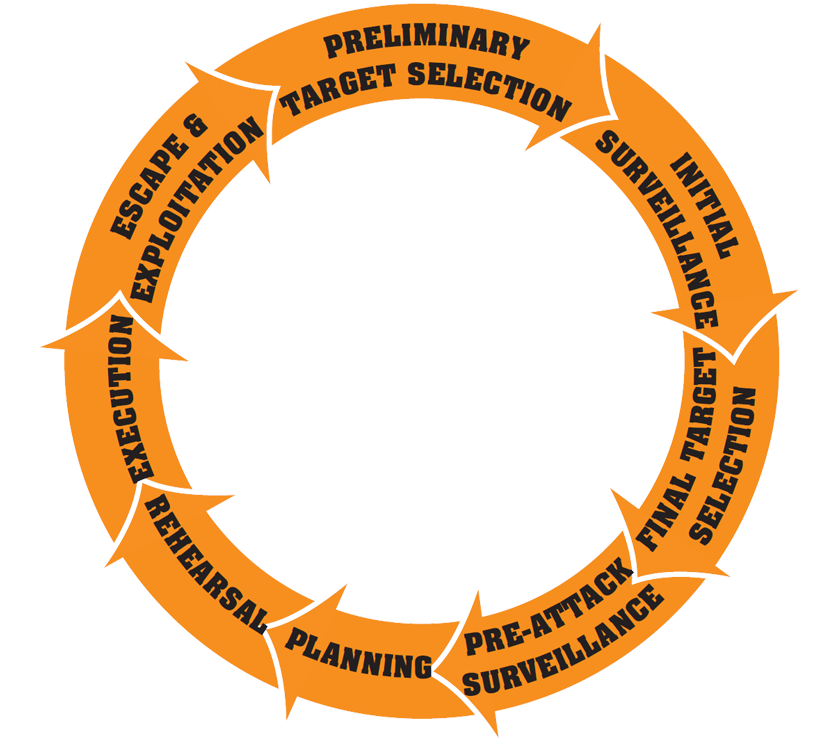
The terrorist attack cycle is the process by which terrorist groups plan and carry out attacks. It begins with the identification of a target and ends with the execution of the attack. Understanding the cycle is crucial for developing effective countermeasures to prevent or disrupt terrorist attacks.
The first step is target selection. Terrorist groups carefully select their targets based on various factors, including the symbolic value of the target, the potential for mass casualties, and the likelihood of media attention. These factors help the group achieve its goals, which may be political, ideological, or religious in nature.
Once a target has been selected, the group begins the planning phase of the attack. This may involve gathering intelligence on the target, acquiring weapons and other resources, and recruiting and training operatives. The planning phase can take weeks, months, or even years, depending on the complexity of the attack.
The execution phase of the terrorist attack cycle involves the actual carrying out of the attack. This may involve the transportation of weapons and operatives to the target, the positioning of explosives or other weapons, and the execution of the attack itself. The execution phase is usually the shortest part of the terrorist attack cycle, but it can have devastating consequences for the victims and the wider society.
After the attack, the group may claim responsibility for the attack and seek to capitalize on the media attention it has generated. This may include releasing statements or videos to justify the attack or to try to gain support from like-minded individuals or groups.
Understanding the terrorist attack cycle is crucial for developing effective countermeasures to prevent them or mitigate the damage. This may involve disrupting the planning phase of the attack through intelligence gathering and law enforcement efforts, or it may involve protecting potential targets through physical security measures or other means. By understanding the terrorist attack cycle, governments and other organizations can take steps to prevent or lessen the impact of terrorism on society.
It is important to note that there is no one specific set of behaviors or activities that can definitively indicate that a terrorist attack is imminent. Indicators of suspicious activity that may be related to a potential terrorist attack include:
1. Suspicious behavior or activities that could be related to planning an attack, such as surveillance, mapping out locations, or acquiring materials that could be used in an attack.
2. Unusual interest in or knowledge of potential targets, such as buildings, infrastructure, or transportation systems.
3. Purchasing or stockpiling weapons or explosives, or attempting to obtain hazardous materials or chemicals.
4. Expressing extremist views or ideology, or expressing support for terrorist organizations or their goals.
5. Making threats or communicating about a potential attack.
6. Displaying unusual behavior or emotional distress, such as being extremely agitated or withdrawn.
It is important to note that many of these behaviors and activities may be related to other criminal or non-terrorist activities, and may not necessarily indicate a pending terrorist attack. It is also important to remember that persons who are planning or involved in terrorism may attempt to conceal their activities and intentions. Remember that if you become aware of an activity that may indicate a pending attack, it may be targeting you.
IMPORTANT KNOWLEDGE THAT MAY FOREWARN OF A FUTURE ATTACK MAY BE DERIVED FROM OBSERVATIONS MADE BY CIVILIANS”
If you recognize suspicious activity that may be linked to terrorism, it is imperative to report it to law enforcement authorities so that it can be properly investigated.
I’m David. Thank you for listening. Our next episode will be Gun Ownership for Self-Defense. Is it the right decision for you? Paid subscribers obtain on-demand access to me as their personal or business consultant. Get quick answers or in-depth discussions about any security or safety issues of concern. It’s a cost-effective way to utilize professional security expertise at your home or business. Remember these words to live by. Don’t Get Dead.